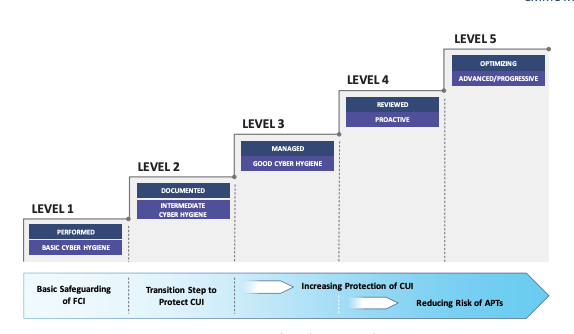
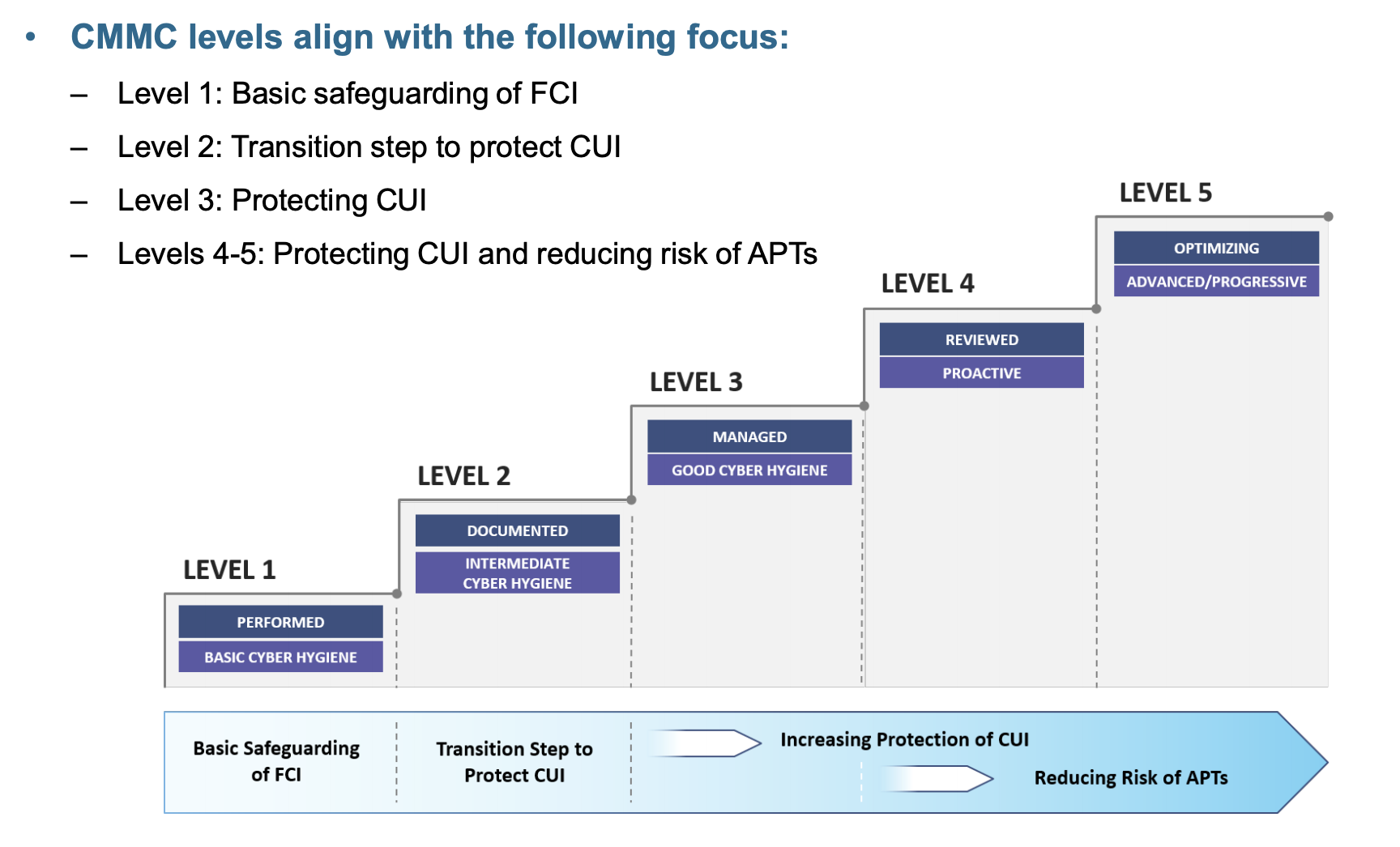
The cybersecurity maturity model certification (CMMC) is a new U.S. Department of Defense requirement for over 300,000 prime and subcontractors. CMMC comes with a new framework of security controls. The framework or model includes requirements for security practices and processes.
CMMC Domains Explained
There are seventeen domains in the CMMC model. Domains define your strategic security objectives for your required security capabilities. For example, the capabilities under the “access control” domain seek to limit access to your systems to authorized persons.
Each domain has multiple capabilities.
CMMC Capabilities Explained
A capability defines a specific requirement to support the objective of a domain. For example, the capability of “establishing system access requirements” supports the “Access Control” domain.
Each capability has practices.
CMMC Practices Explained
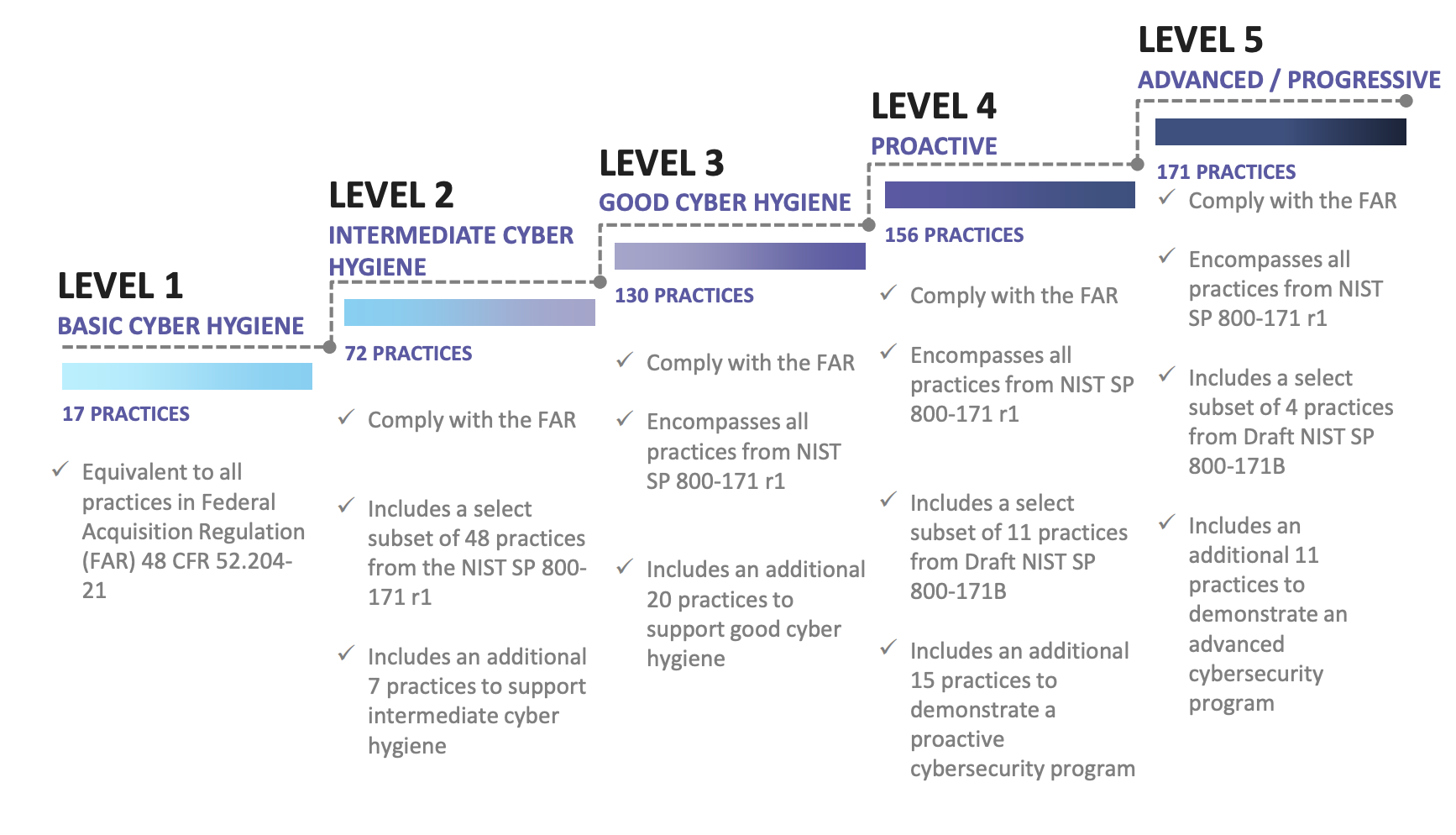
Practices are the specific security requirements you need to implement. Practices support the implementation of capabilities. Practices are the security controls you are required to implement. Each CMMC level has a specific number of practices that need to be implemented.
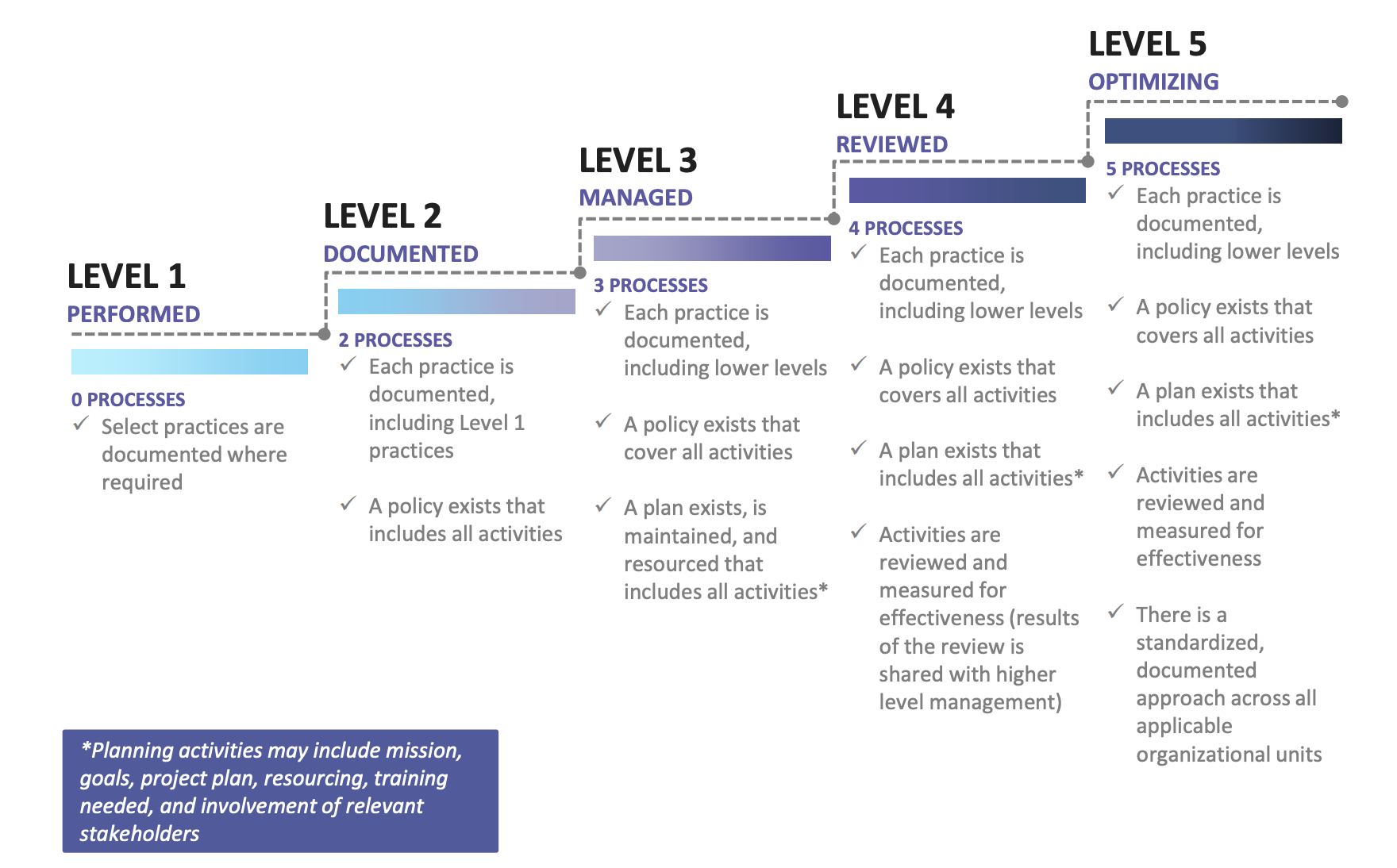
CMMC Processes Explained
Processes define the maturity level at which a practice has been implemented. For example, your company may have implemented password length and complexity as required by a CMMC practice. If the password requirements have not been documented the practice isn’t mature. There is no way to guarantee that the password requirements will be consistently implemented. However, if you were to implement your password requirements, document them in a policy, and create a plan to implement them on all of your systems the implementation of that practice would be more mature.
Processes are critical to improving the maturity of CMMC practices.
How CMMC Maturity Levels Relate to CMMC Practices & Levels
The cybersecurity maturity model certification has five levels. The lowest level has the least amount of security requirements. The higher the level the more security controls aka “practices” you need to implement. Not only do you have to implement more practices but you have to “institutionalize” them. The way process institutionalization or maturity is achieved is by documenting, planning, reviewing, and optimizing your CMMC practices.